So what Is Tokenization?
Payment tokenization is a security technology standardized by EMVCo where sensitive card information is replaced with a unique digital identifier called a token. This way, payments can be processed without exposing card data. The token is unique for a combination of card, token requestor, and merchant.
A significant benefit of tokenization is the fact that a token is only valid in a specific context. This may be a mobile device, a smartwatch, or a particular merchant. Outside the specific area, the token is useless and cannot be misused. In practice, this means that a card account can have multiple tokens used for different purposes e.g one token for your mobile wallet, one token used in your smartwatch, and one token for a streaming service or travel ticket app.
How does Tokenisation Ensure Security?
- Secure Way to store Card Information Currently, the merchants store the Card information in an encrypted system. But Data breaches are very common across most brands. In 2013, Target lost the credit card, debit cards, and other information of tens of millions of customers. In 2018, Marriott disclosed a data breach that impacted up to 500 million people a few such examples. The shift from traditional card payments to digital card payments
- A continually growing number of people use mobile phones, wearables, and online and in-app payments daily to pay for goods and services.
- Management of Card in multiple channels Currently knowing where all your card information is stored is impossible. Managing information of your cards and subscription on multiple platforms is the need of the hour.
How does tokenization work?
Before we start with how tokenization works, let’s understand some keywords: Token Requestor — is the common name for all wallets that requests payment tokens in return for a payment card. TSP (Token Service Provider) — TSPs are the entities that generate the token and securely keep the mapping towards the PAN. Issuer — Entity who issues credit cards (the Bank information on your Card) Acquirer — Entity who accepts payments (via POS Terminal or PG)
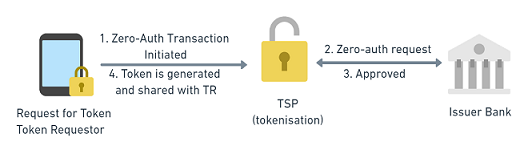
Generating a Token
- Token requestor Sends a request to the TSP for Tokenisation.
- Before the TSP creates a token, the TSP verifies the Card Details via the Zero-Auth Transaction to the issuer.
- The issuer verifies the card information and provides a go-ahead to the TSP to generate a token.
- Once the token is generated by the TSP the token information gets stored on the Token Requestor DB.
CoFT (Card on File Transaction)
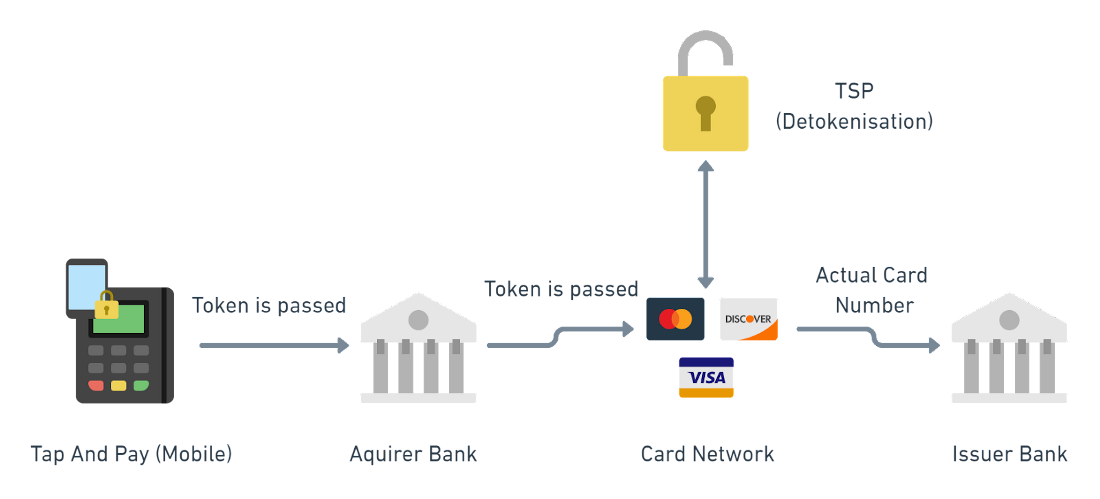
- A Transaction that is initiated by tokenized card is known as CoFT.
- When a transaction is initiated at a terminal (POS or PG), the token information is sent to the Acquirer for Payment Authorization.
- Post that the request is sent to the Card Network which acts as the TSP. Here the TSP performs the Detokenisation process.
- In post Detokenisation process, the Actual card number is forwarded for Payment Authorization.
- The issuer performs various checks (Token information, Account Status, credit balance, etc.) and approves or declines the payment authorization request.
Note: If you look closely, the actual card number is not shared anywhere between the Payment terminal, acquirer, and the Card network.
This is how tokenization secures your card information and creates an additional layer of security to make transactions more secure. With RBI guidelines (in India) this will be mandatory from 30th June 2022 for all merchants to store your card information in tokens. So make sure that you keep an eye on the payments section of all your favorite merchants.
We at Nuclei, are building Issuer Tokenisation Solutions for banks and learning more about issuer tokenization and the role it will play in the future of Finance. We are seeking out individuals who have experience or knowledge in this area to have a virtual chat and exchange ideas.
If you're interested in discussing Issuer Tokenization, please connect with us at cards@gonuclei.com
